Home • Регистрация • FAQ • Поиск • Вход |
| Сообщения без ответов | Активные темы | Текущее время: 23 апр 2021, 04:25
|
Страница 1 из 1
| [ Сообщений: 4 ] |
| Версия для печати | Пред. тема | След. тема |
| Автор | Сообщение |
|---|
Зарегистрирован: 01 янв 1970, 03:00
Сообщения: 2
| после того как я подкличаюсь vpn client-ом . через какоето время сесия зависает и больше даже не пингует внешни interface asa 5505
| | 12 май 2011, 14:39 |
Зарегистрирован: 01 окт 2008, 12:24
Сообщения: 4436
| Подключаетесь снаружи?
Split-tunnel настроен?
Опишите проблему подробнее. С настройками, желательно
| | 12 май 2011, 16:01 | да. с наружи подключаюсь.
ciscoasa# sh run
: Saved
:
ASA Version 7.2(3)
!
hostname ciscoasa
domain-name agd
enable password FDNjnHzqds9oJpSX encrypted
names
!
interface Vlan1
nameif inside
security-level 100
ip address 192.168.87.2 255.255.255.252
!
interface Vlan2
nameif outside
security-level 0
ip address xxx.xxx.xxx.xxx 255.255.255.248
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
passwd FDNjnHzqds9oJpSX encrypted
banner exec DA ERNESTS
banner login AKOCET OTARAS TRAKZE
ftp mode passive
dns domain-lookup inside
dns domain-lookup outside
dns server-group DefaultDNS
name-server 192.168.80.32
domain-name agd
access-list inside_nat0_outbound extended permit ip any 192.168.88.0 255.255.255.224
access-list inside_nat0_outbound extended permit ip any host 192.168.88.100
pager lines 24
logging enable
logging asdm informational
mtu inside 1500
mtu outside 1500
ip local pool 123456 192.168.88.2-192.168.88.20 mask 255.255.255.0
ip local pool giga 192.168.88.100 mask 255.255.255.0
icmp unreachable rate-limit 1 burst-size 1
asdm image disk0:/asdm-523.bin
no asdm history enable
arp timeout 14400
nat-control
nat (inside) 0 access-list inside_nat0_outbound
route inside 192.168.80.0 255.255.255.0 192.168.87.1 1
route inside 10.10.0.0 255.255.0.0 192.168.87.1 1
route outside 0.0.0.0 0.0.0.0 213.131.41.177 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout uauth 0:05:00 absolute
http server enable
http 192.168.80.2 255.255.255.255 inside
http 192.168.80.0 255.255.255.0 inside
http authentication-certificate inside
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec transform-set CLIENT_TS esp-aes esp-sha-hmac
crypto ipsec transform-set ESP-3DES-SHA esp-3des esp-sha-hmac
crypto dynamic-map DYN_CLIENTS 10 set transform-set CLIENT_TS
crypto dynamic-map DYN_CLIENTS 30 set pfs
crypto dynamic-map DYN_CLIENTS 30 set transform-set ESP-3DES-SHA
crypto dynamic-map DYN_CLIENTS 50 set pfs
crypto dynamic-map DYN_CLIENTS 50 set transform-set ESP-3DES-SHA
crypto dynamic-map DYN_CLIENTS 70 set pfs
crypto dynamic-map DYN_CLIENTS 70 set transform-set ESP-3DES-SHA
crypto dynamic-map DYN_CLIENTS 90 set pfs
crypto dynamic-map DYN_CLIENTS 90 set transform-set ESP-3DES-SHA
crypto dynamic-map DYN_CLIENTS 110 set pfs
crypto dynamic-map DYN_CLIENTS 110 set transform-set ESP-3DES-SHA
crypto dynamic-map DYN_CLIENTS 130 set pfs
crypto dynamic-map DYN_CLIENTS 130 set transform-set ESP-3DES-SHA
crypto dynamic-map DYN_CLIENTS 150 set pfs
crypto dynamic-map DYN_CLIENTS 150 set transform-set ESP-3DES-SHA
crypto dynamic-map DYN_CLIENTS 170 set pfs
crypto dynamic-map DYN_CLIENTS 170 set transform-set ESP-3DES-SHA
crypto dynamic-map DYN_CLIENTS 190 set pfs
crypto dynamic-map DYN_CLIENTS 190 set transform-set ESP-3DES-SHA
crypto dynamic-map DYN_CLIENTS 210 set pfs
crypto dynamic-map DYN_CLIENTS 210 set transform-set ESP-3DES-SHA
crypto dynamic-map DYN_CLIENTS 230 set pfs
crypto dynamic-map DYN_CLIENTS 230 set transform-set ESP-3DES-SHA
crypto map CLIENTS 10 ipsec-isakmp dynamic DYN_CLIENTS
crypto map CLIENTS interface outside
crypto isakmp enable outside
crypto isakmp policy 20
authentication pre-share
encryption 3des
hash md5
group 2
lifetime 86400
crypto isakmp policy 40
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 86400
crypto isakmp nat-traversal 20
telnet 192.168.80.36 255.255.255.255 inside
telnet 192.168.80.2 255.255.255.255 inside
telnet 192.168.80.1 255.255.255.255 inside
telnet 10.10.8.16 255.255.255.255 inside
telnet timeout 5
ssh 213.131.41.178 255.255.255.255 outside
ssh timeout 5
console timeout 0
dhcpd auto_config outside
!
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
!
service-policy global_policy global
group-policy nova_branches internal
group-policy nova_branches attributes
dns-server value 192.168.80.32
vpn-tunnel-protocol IPSec
group-policy 123456 internal
group-policy 123456 attributes
vpn-tunnel-protocol IPSec
group-policy giga internal
group-policy giga attributes
dns-server value 192.168.80.32
vpn-tunnel-protocol IPSec
username nova_qutaisi password kvcjN06FXjbhm5/Z encrypted privilege 0
username nova_qutaisi attributes
vpn-group-policy nova_branches
username nova_batumi password vSbFHoH58KGQwilw encrypted privilege 0
username nova_batumi attributes
vpn-group-policy nova_branches
username 123456 password P8dZ7nOjjJPDoTgI encrypted privilege 0
username 123456 attributes
vpn-group-policy 123456
username rachman password bU7Hh2k3HcDlOqs1 encrypted
username r.manukian password /s5sq78eof7LS/Pf encrypted privilege 0
username r.manukian attributes
vpn-group-policy nova_branches
username r.mkrtichian password PDuMyce1i8ThElbu encrypted
username giga password dZP2ii/P3kXRqE4C encrypted privilege 0
username giga attributes
vpn-group-policy giga
tunnel-group 123456 type ipsec-ra
tunnel-group 123456 general-attributes
address-pool 123456
default-group-policy 123456
tunnel-group 123456 ipsec-attributes
pre-shared-key *
tunnel-group nova_branches type ipsec-ra
tunnel-group nova_branches general-attributes
address-pool 123456
default-group-policy nova_branches
tunnel-group nova_branches ipsec-attributes
pre-shared-key *
tunnel-group giga type ipsec-ra
tunnel-group giga general-attributes
address-pool giga
default-group-policy giga
tunnel-group giga ipsec-attributes
pre-shared-key *
tunnel-group r.manukian type ipsec-ra
tunnel-group r.manukian general-attributes
address-pool 123456
default-group-policy nova_branches
tunnel-group r.manukian ipsec-attributes
pre-shared-key *
prompt hostname context
Cryptochecksum:84aaeaee52ba1be3836b85de673e5240
: end
| | 13 май 2011, 12:33 |
Зарегистрирован: 01 окт 2008, 12:24
Сообщения: 4436
| Вы к какой группе цепляетесь?
Насколько я вижу, никакого split-tunnel нет. Значит после подключения ВСЕ пакеты идут в туннель. Включая и пакеты, которые вы пытаетесь отправить на адрес самой асашки. (тот самый пинг, который не проходит)
| | 13 май 2011, 21:35 |
Страница 1 из 1
| [ Сообщений: 4 ] |
Кто сейчас на конференции | Сейчас этот форум просматривают: Google [Bot] и гости: 16 |
Вы не можете начинать темы
Вы не можете отвечать на сообщения
Вы не можете редактировать свои сообщения
Вы не можете удалять свои сообщения
Вы не можете добавлять вложения
|
Создано на основе phpBB® Forum Software © phpBB Group
Designed by ST Software for PTF.
Русская поддержка phpBB |
- 3Gateway Configuration
- 4Client Configuration
Introduction
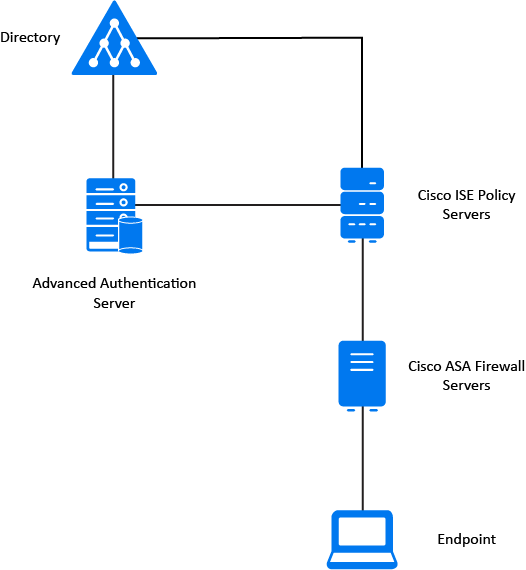
This guide provides information that can be used to configure a Cisco PIX/ASA device running firmware version 7.x to support IPsec VPN client connectivity. If you have a PIX device running firmware version 6.x, please consult the HowtoCiscoPix. The Shrew Soft VPN Client has been tested with Cisco products to ensure interoperability.
Overview
The configuration example described below will allow an IPsec VPN client to communicate with a single remote private network. The client uses the pull configuration method to acquire the following parameters automatically from the gateway.
See how to configure a Cisco ASA / PIX Easy VPN Client connection in 1 minute. Make your life easy by setting up a VPN using software from. In the diagram above, when a remote VPN client connects (via VPN) to the ASA, it should have access to the LAN behind the ASA. This is standard remote access VPN and can be achieved with the following configuration on the ASA.
- IP Address
- IP Netmask
- DNS Servers
- DNS Default Domain Suffix
- DNS Split Network Domain List
- WINS Servers
- PFS Group
- Remote Network Topology
- Login Banner
Gateway Configuration
This example assumes you have knowledge of the Cisco ASA gateway command line configuration interface. For more information, please consult your Cisco product documentation.
Interfaces
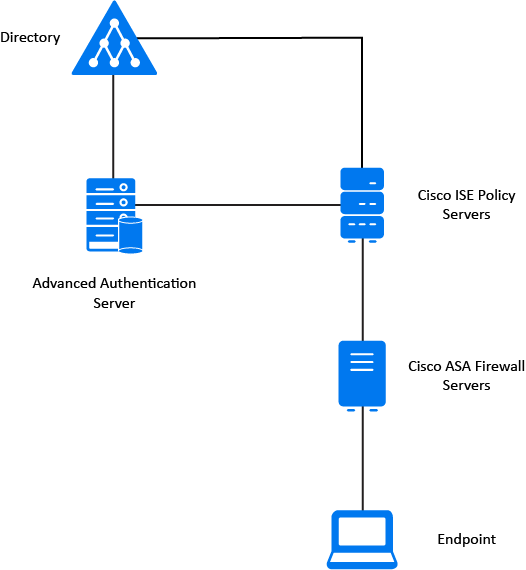
Two network interfaces are configured. The outside interface has a static public IP address of 1.1.1.20 which faces the internet. The inside interface has a static private IP address that faces the internal private network. The default gateway is configured as 1.1.1.3 via the outside interface.
Access List
An access lists must be configured to define the IPSec policies. This is expressed with the source matching the local private network(s) and the destination matching any as the VPN client address will be assigned by the gateway.
Address Pool
The IP address pool must be configured. Clients will be assigned private network addresses from a pool of 10.2.20.1-10.2.20.126.
User Authentication
User authentication must be configured to support IKE extended authentication ( XAuth ). In this example, we use define user accounts locally on the ASA. It is possible to pass this authentication to a radius or an LDAP account server using the Cisco AAA authentication mechanism. For more information, please consult your cisco product documentation.
IPsec Parameters
A transform set and dynamic IPsec crypto map must be configured to support client VPN connections. The dynamic crypto map is then assigned to a standard crypto map and bound to the outside ( public ) interface. Dish anywhere download mac.
ISAKMP Parameters


The ISAKMP protocol must be enabled on the outside ( public ) interface and an ISAKMP policy must be configured. NAT Traversal is also enabled to allow clients to communicate effectively when their peer address is being translated. The keep alive packet rate is set to 20 seconds.
Group Policy
A group policy must be configured to provide the client with dynamic configuration information.
Tunnel Group
A tunnel group must be configured to define the VPN Client tunnel parameters. It is created using the type ipsec-ra for IPsec remote access. The client uses the tunnel group name as its FQDN identity value and the tunnel group pre-shared-key as its pre-shared key value.
Client Configuration
The client configuration in this example is straight forward. Open the Access Manager application and create a new site configuration. Configure the settings listed below in the following tabs.
Cisco Asa Vpn Client Download
General Tab
The Remote Host section must be configured. The Host Name or IP Address is defined as 10.1.1.20 to match the ASA outside ( public ) interface address. The Auto Configuration mode should be set to ike config pull.
Phase 1 Tab
The Proposal section must be configured. The Exchange Type is set to aggressive and the DH Exchange is set to group 2 to match the ASA ISAKMP policy definition.
Authentication Tab
The client authentication settings must be configured. The Authentication Method is defined as Mutual PSK + XAuth.
Asa Vpn Config
Local Identity Tab
The Local Identity parameters are defined as Fully Qualified Domain Name with a FQDN String of 'vpnclient' to match the ASA tunnel group name. Canon utility software download mac.
Remote Identity Tab
The Remote Identity parameters are set to IP Address with the Use a discovered remote host address option checked to match the ASA ISAKMP identity parameter.
Credentials Tab

The Credentials Pre Shared Key is defined as 'mypresharedkey' to match the ASA tunnel group pre-shared-key.
Known Issues
Cisco gateways support a proprietary form of hybrid authentication which does not conform to RFC draft standards. At this time the Shrew Soft VPN Client does not support this authentication mode. We hope to add support for this in the future.
Resources
Media:Ciscoasa.cfg.txt
Media:Ciscoasa.vpn.txt
Retrieved from 'https://www.shrew.net/support/index.php?title=Howto_Cisco_Asa&oldid=339'